Given the huge revenues at stake and the high net worth of some sportspeople, the global sports industry is a particularly attractive target for cyber criminals. Sports organisations, competitive teams, individual players and even fans are vulnerable to a range of cyberattacks including competitor espionage, ransomware, and social engineering. Teams, broadcasters, merchandisers and advertisers hold a large amount of sensitive data, which if stolen by bad actors, could have serious repercussions.
Digitisation in sports
Like all industries, sport has become increasingly digitised over the last decade. Technology is being used to improve engagement with fan bases through social media, to sell tickets, and to provide team news and updates. The coronavirus has accelerated this digitisation in all sectors, but sports has been particularly challenged; lacking the physical means to interact, fans are demanding more and better ways of engaging online.
This growing reliance on technology creates more avenues for cybercriminals to target and obtain sensitive data. For example, sports fans signing up to paid services such as live streaming provide their credit card details and other personally identifiable information (PII). If sufficient security measures are not in place, this data is vulnerable to being stolen by bad actors and used for cyber fraud.
Data extortion and ransomware
Sports teams and organisations hold large amounts of personal data such as medical records, sponsorship deals, contact information and salary information. This information is valuable to attackers, making sports organisation an enticing target for financially-motivated cyber criminals. Aside from this data, personal and sensitive information regarding the many high-net worth individuals in the sports industry is also a target. Groups such as “The Dark Overlord” have extorted high-profile targets for large ransoms, and have been known to sell their victim's data on dark web marketplaces .
Ransomware is a type of malware that infects the victim's systems, blocking access and hijacking files until a ransom is paid. Mainstream media organisations which then publicise the results of successful attacks further exacerbate their impact. Encouraged by the success of such ransomware groups, many of these criminal gangs are now demanding two ransoms: one for unlocking the encrypted files, and a second to not publish any of the stolen data.
Recently, the REvil ransomware group targeted New York law firm Grubman Shire Meiselas & Sacks. They published teasers of the highly sensitive information they claimed to have stolen in order to pressure the firm into paying the ransom, before auctioning off the data on the dark web (Figure 1).
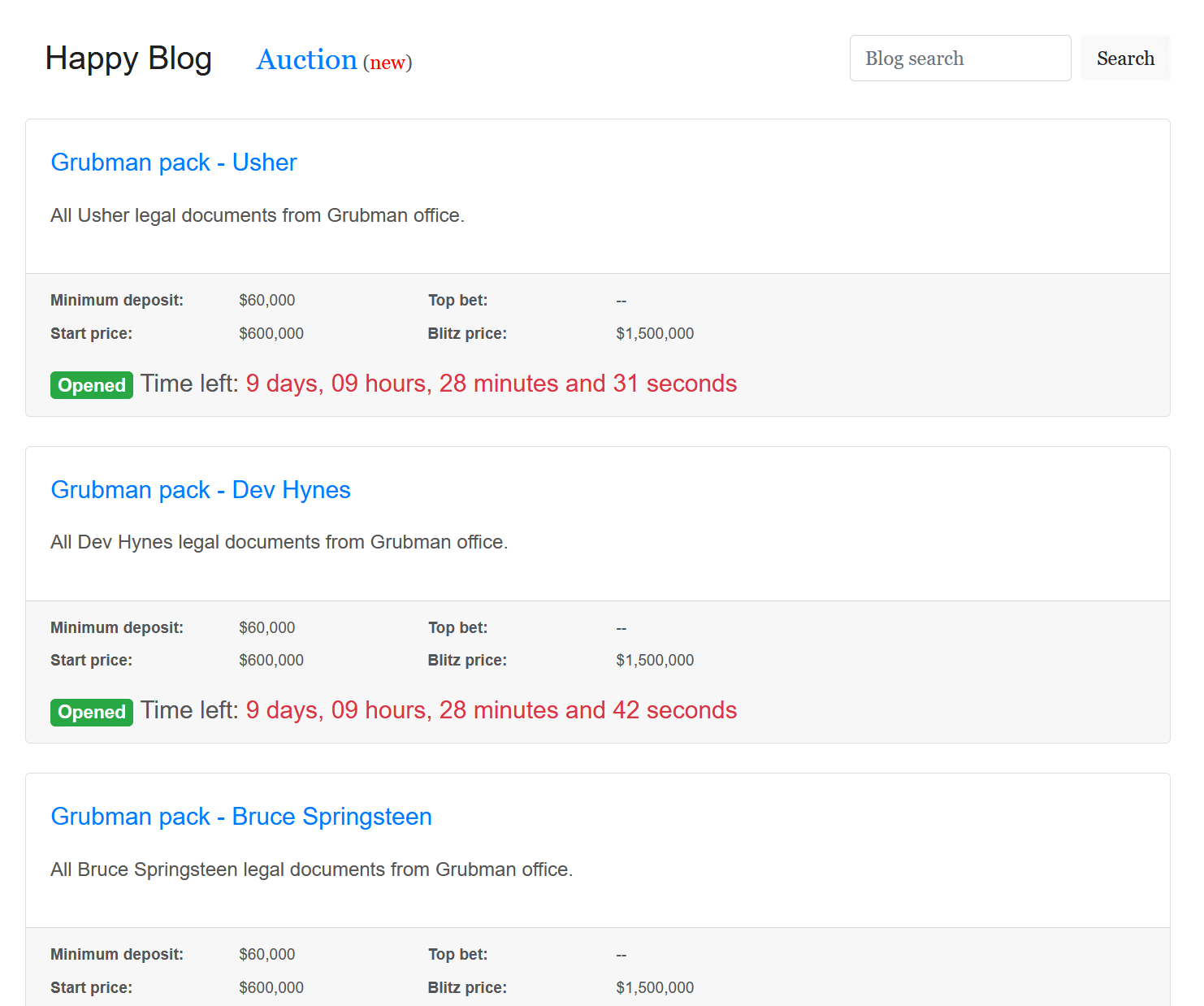
Figure 1: REvil auction page of stolen sensitive data
Phishing
Another tactic used by cyber criminals is social engineering through phishing emails. Phishing emails are used to solicit sensitive confidential information by imitating a trustworthy source. For example, in 2016, members of the NBA's Milwaukee Bucks' tax and income information was exposed after an employee fell for an email purporting to be the team's President asking for the data. Business email compromise (BEC) scams are commonplace and reportedly led to USD 1.7 billion in losses in 2019 .
Insider and competitor threat
Whilst sports teams and organisations are vulnerable to the same cyber attacks as other industries, they are also vulnerable to insider threats and those posed by competitors. Other teams trying to gain a competitive advantage have been known to infiltrate online systems to view information about game plans, potential trades and player performance.
Such was the case in 2013 when the Major League Baseball team the Houston Astros had their internal discussions, player statistics and other sensitive information publicly leaked. The FBI and US Justice Department traced the source of the leak to Astros rival team, the St Louis Cardinals. In a relatively unsophisticated move, the Cardinals infiltrated the network using the credentials of a former Cardinals manager who had then moved over to Astros. This demonstrates the risk of sports teams to corporate espionage and highlights the need for secure and unique passwords.
Mitigation
Cybersecurity should be at the forefront of every business and organisation, especially as more employees are working remotely during the coronavirus pandemic. Securing these organisations' online infrastructure is imperative to protecting them against harmful data leaks and cyber attacks.
As was seen in the compromise of the Astro's database, weak passwords can put organisations at risk. The introduction of fundamentals such as multi-factor authentication, the careful review and restriction of data access, and the establishment of a good cyber security baseline can help to mitigate the risks of a breach. Importantly, organisations should also back up their data so that in the event of a breach that destroys data, any data that is lost can be recovered.
Unsurprisingly the weaknesses inherent in passwords play a role. Passwords need to be designed out where possible, if that’s not possible then the use of technical measures such as account lockouts and enhanced monitoring are recommended. Help users cope with password overload by using password managers and preventing them from picking passwords that are already breached.
When a data leak does occur, we recommend that communications, marketing and legal teams are engaged as early as possible if publication of the data is likely . A coordinated response strategy is needed to enable consistency in an evolving situation. Alongside this, if the stolen information is covered by legal privilege or may be damaging, court orders can prevent some publication.
Sports clubs can also mitigate the risks to players also by ensuring their digital online privacy is reviewed. Player accounts may be at risk of hacking attempts if not adequately protected. Social media accounts should be made as private as possible to ensure personal information is not revealed which could be used against individuals such as locations, physical addresses, email addresses and passwords.
MDR Cyber assist sports clients in ensuring they have good cybersecurity strategies and can help respond to cyber attacks, frauds or extortion, should the worst happen. We also help protect the online privacy and security of key team-members. Our investigations are enhanced by our close access to our Mishcon legal teams. To find out more, email cyber@mishcon.com.